ANTIDRONE GLOBAL SYSTEM
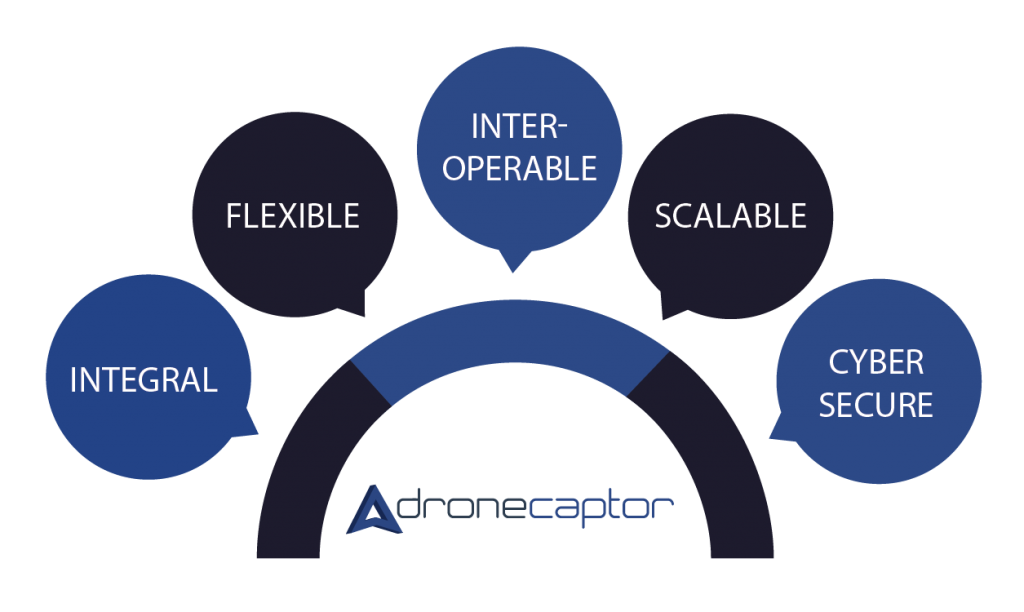
Scalable, flexible and automated solution, commanded from a remote control center. ALERTS are managed and DECISIONS taken accordingly to different threats and scenarios

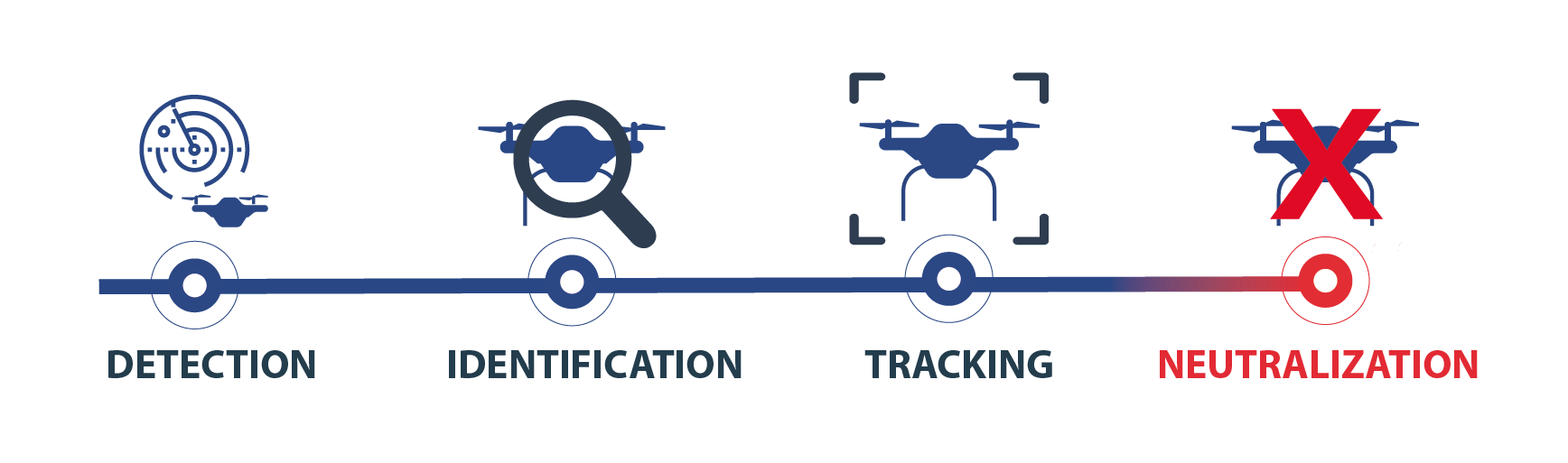
DETECTION: Early detection system of UAVs
IDENTIFICATION: System that recognizes, identifies and classifies each drone
TRACKING: Monitoring route and position of the threat
NEUTRALIZATION: Drone-specific neutralization system
IDENTIFICATION: System that recognizes, identifies and classifies each drone
TRACKING: Monitoring route and position of the threat
NEUTRALIZATION: Drone-specific neutralization system
INTELLIGENCE
Dronecaptor reliably detects and neutralizes unauthorized drones (UAVs) combining multiple sensors, automatically analysing all the information received from each of them. It permits actions coordinated against multiple threats.The system has ability to:
- Filtering and Combining
- Friendly drone whitelist
- Automatically analisy all the information received
- Providing early threat detection
- Higher level of recognition accuracy
OPERATION
- Global Command & Control Centre for a coordinated action of the integrated devices- Allows the phased integration of devices
- Is fully adaptable to operational requirements
- Improving the response against an intruder drone
- Automated mechanisms based on behavioural rules and operational protocols predefined by the user
SCENARIOS: